The Truth Behind Counterfeit Stock — The Local Artisan Guide
$ 175.50 Buy It Nowor Best Offer, FREE Shipping, 30-Day Returns
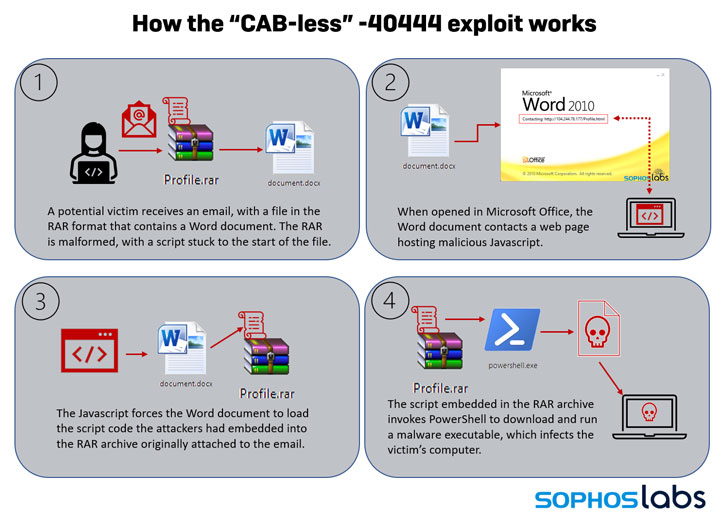
New Exploit Lets Malware Attackers Bypass Patch for Critical - vulnerability database
Grossman LLP, Art Law Blog
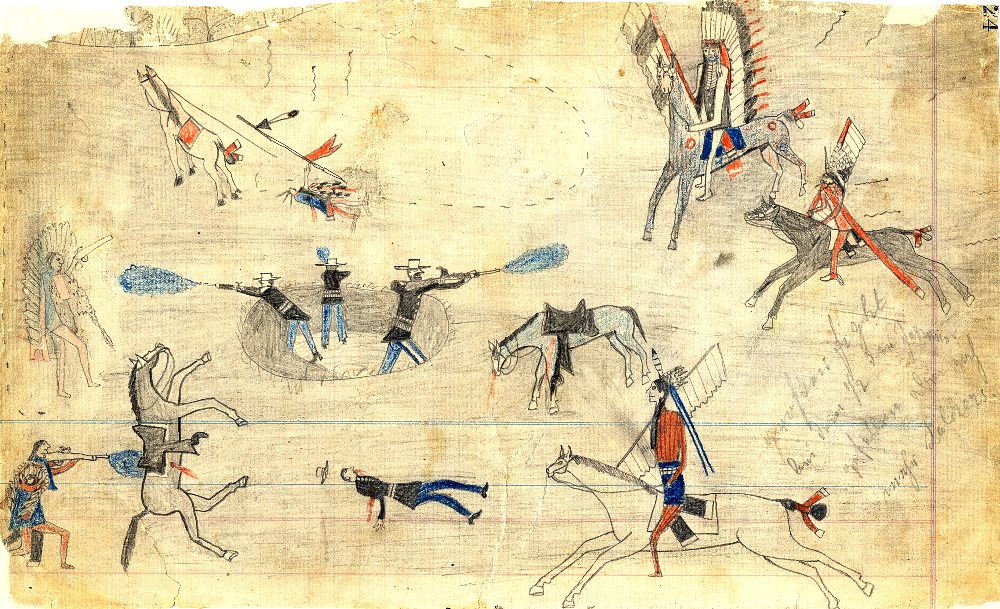
How Possibly Fraudulent and Forged Indigenous Art Ends up in Museums
website/links.json at gh-pages · academia-de-ursarie/website · GitHub

Threat Analysis: Equation Equals Backdoor - vulnerability database
cs224u-fp/data/kaggle/dev.csv at master · sebschu/cs224u-fp · GitHub
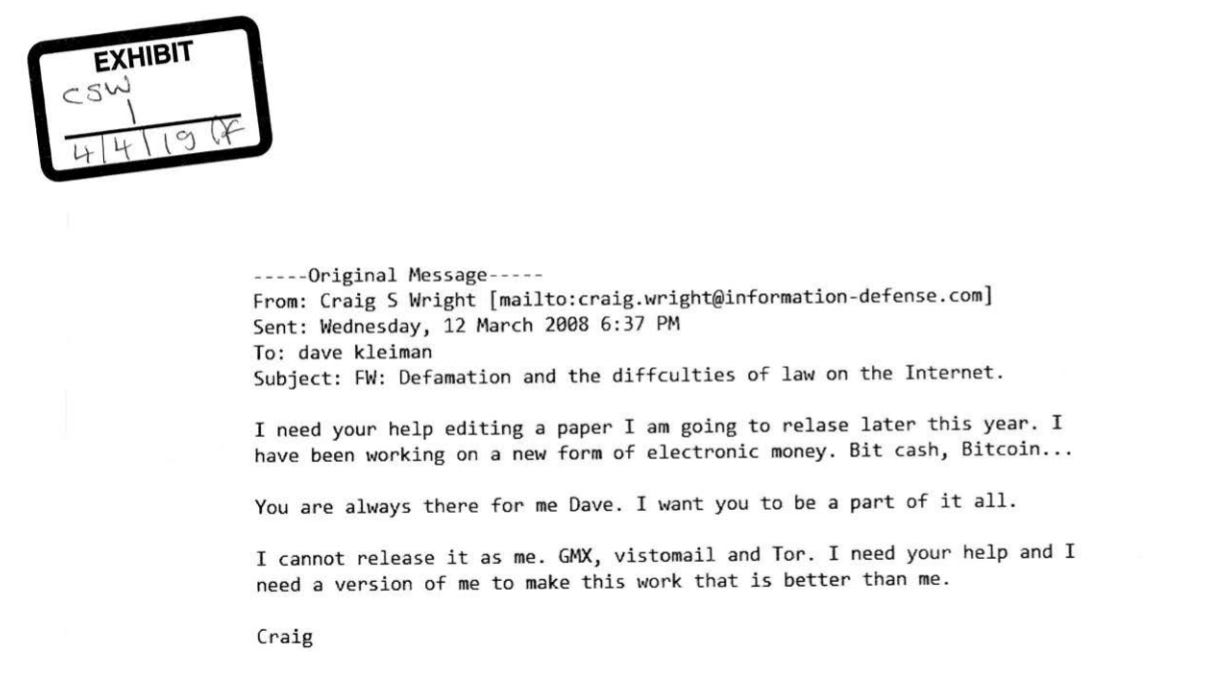
Faketoshi, The Early Years — Part 1, by MyLegacyKit
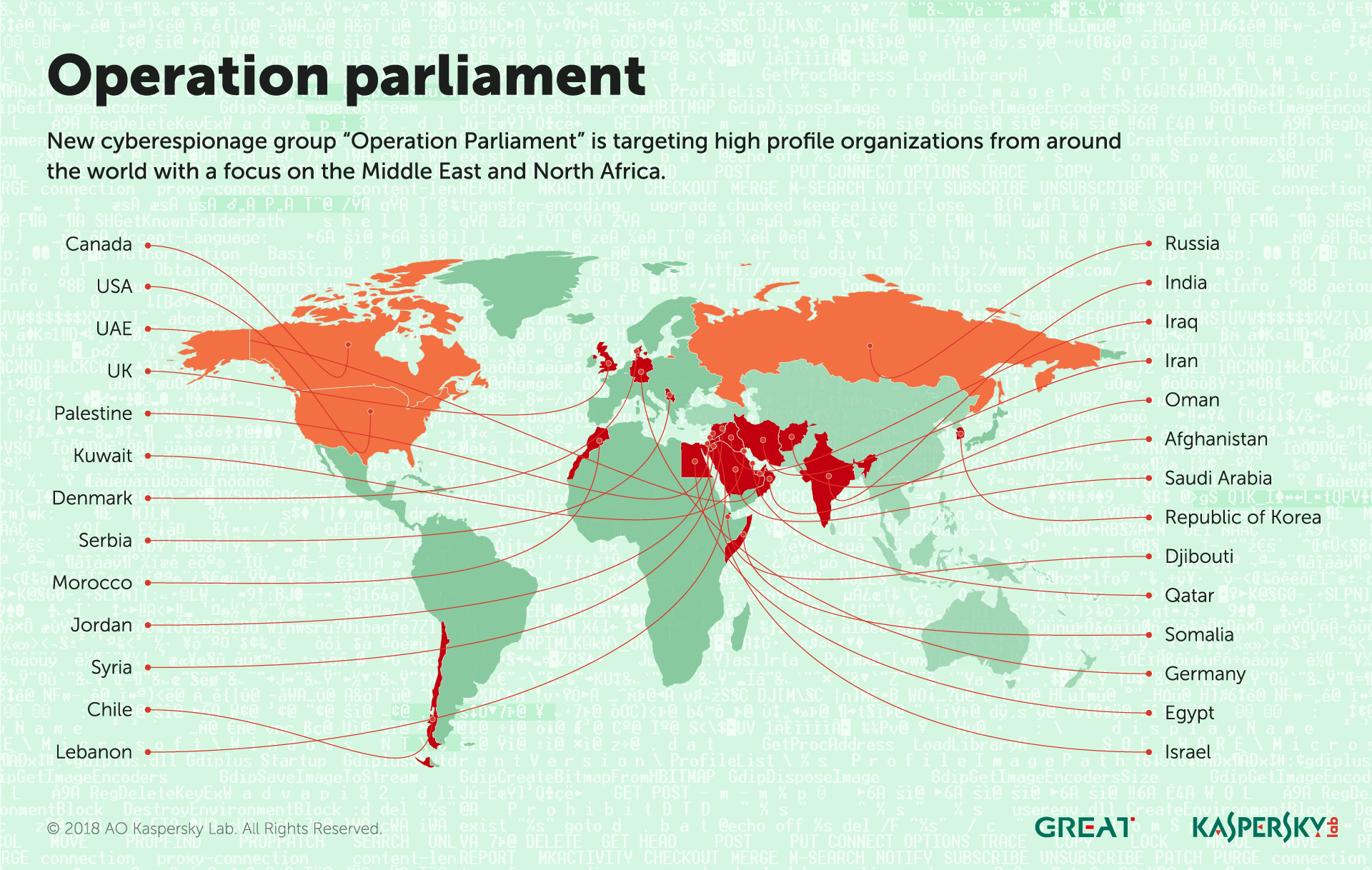
IT threat evolution Q2 2018 - vulnerability database

Fakes-Forgeries
The Truth Behind Counterfeit Stock — The Local Artisan Guide
- Best Price $ 175.50. Good quality and value when compared to simondewaal.eu similar items.
- Seller - 730+ items sold. Top-Rated Plus! Top-Rated Seller, 30-day return policy, ships in 1 business day with tracking.
People Also Loved
-

Authenticated Used Louis Vuitton Monogram Solar Ray Soft Trunk
Buy It Now 5d 22h -

Louis Vuitton Trio Backpack Travel Bag M44658 Gold Chain
Buy It Now 6d 22h -

Louis Vuitton Fornasetti Speedy 25 Bandouliere
Buy It Now 23d 23h -

Louis Vuitton Speedy Bandoulière 25 Brown Monogram
Buy It Now 18d 13h -

Louis Vuitton Louis Vuitton Andrei Black Taiga Leather Messenger Bag
Buy It Now 22d 17h -

Louis Vuitton Black Leather Empreinte Monogram Key Pouch (w/ Dust
Buy It Now 27d 15h -
/spree/images/attachments/005/177/834/original/louis-vuitton-2000-pre-owned-musette-tango-shoulder-bag-brown-farfetch-photo.jpg)
Louis Vuitton 2000 pre-owned Musette Tango shoulder bag
Buy It Now 9d 23h -

Krug Logo transparent PNG - StickPNG
Buy It Now 15d 16h -

Louis Vuitton Caramel Monogram Wild at Heart Toiletry Pouch 26
Buy It Now 25d 16h -

Louis Vuitton Palm Springs Mini Backpack For Sale at 1stDibs louis vuitton backpack mini, louis vuitton small backpack, mini lv backpack
Buy It Now 8d 8h -

Louis Vuitton Trainer Sneaker by Virgil Abloh #54 BLUE UK Size 10
Buy It Now 25d 15h -

Unboxing Louis Vuitton Nice MINI Toiletry Pouch
Buy It Now 7d 15h -

Supreme X Louis Vuitton Barber Cape
Buy It Now 15d 19h -

Louis Vuitton 2018 Pre-owned Lymington Damier Azur Tote Bag - Neutrals
Buy It Now 24d 10h -
Coach Sport Flat Leather Card Case
Buy It Now 4d 22h -

Can Virgil Abloh Fit in a Museum? - The New York Times
Buy It Now 7d 11h -

Louis Vuitton, Bags, Louis Vuitton Nocturne Epi Leather Vintage Bag
Buy It Now 24d 6h -

Goyard Bourget PM Trolley Suitase Black
Buy It Now 22d 23h -

Anemone Kelly 25 Retourne Togo leather, Shades of purple, Hermes
Buy It Now 4d 6h -
Popoholic » Blog Archive » Chloe Grace Moretz Looking Like A Cute… Fashion Disaster
Buy It Now 18d 16h -

LOUIS VUITTON Authentic Paper Gift Shopping Bag Orange Sm 8.5 X 7 X 4.5”
Buy It Now 26d 16h -

Bag > Louis Vuitton Why Knot PM
Buy It Now 28d 8h -

Louis-Vuitton-Set-of-2-Monogram-Long-Wallet-Brown-M61725 – dct-ep_vintage luxury Store
Buy It Now 20d 7h -

Gafas LOUIS VUITTON Louis vuitton, Gafas
Buy It Now 26d 13h
