Lv Hot Ski Mask – Bel9 by Denly
$ 314.00 Buy It Nowor Best Offer, FREE Shipping, 30-Day Returns
AvosLocker Ransomware Behavior Examined on Windows & Linux

Hackers Exploit Log4j Vulnerability to Infect Computers with

Hair Accessories – Bel9 by Denly

Imperva Observes Hive of Activity Following Hafnium Microsof
National Greyhound Review - Summer 2018 by Leslie Csokasy - Issuu

Ransomware-as-a-service: Understanding the cybercrime gig ec
Clouds, Clocks, and Sitting at Tables – Page 2 – A blog about
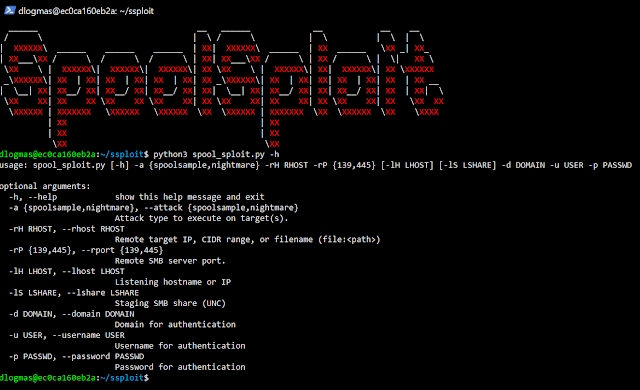
SpoolSploit - A Collection Of Windows Print Spooler Exploits

The Art of FOH Mixing: On Tour with Maluma - Waves Audio
Lv Hot Ski Mask – Bel9 by Denly
- Best Price $ 314.00. Good quality and value when compared to simondewaal.eu similar items.
- Seller - 660+ items sold. Top-Rated Plus! Top-Rated Seller, 30-day return policy, ships in 1 business day with tracking.
People Also Loved
-

Real or Fake? Louis Vuitton Palm Springs Backpack – My Closet Rocks
Buy It Now 8d 20h -

LVMH Bags Rimowa to Bolster Luxury Luggage Range - WSJ
Buy It Now 11d 15h -
LOUIS VUITTON LV Monogram Keepall 50 Bandouliere Travel Bag
Buy It Now 22d 13h -

Four Louis Vuitton Crossbody Bags You Need Now
Buy It Now 19d 11h -

Louis Vuitton Pre-owned Dots Infinity Yayoi Kusama Trench Coat
Buy It Now 21d 5h -

LOUIS VUITTON Neonoe MM 2 Way Bag M46029 Arizona Beige Hand Shoulder Purse Ex++
Buy It Now 22d 19h -

Louis Vuitton Black Giant Monogram Empreinte Onthego PM Gold Hardware, 2022 (Like New), Womens Handbag
Buy It Now 20d 10h -

Vintage Louis Vuitton brown monogram key case. Classic unisex
Buy It Now 15d 7h -

Louis Vuitton® Neo Wallet Trunk Monogram. Size in 2023
Buy It Now 17d 17h -

Louis Vuitton Navy Monogram Shadow Leather Sprinter Backpack Black
Buy It Now 28d 15h -

Philippe LACOMBE - Photographer
Buy It Now 8d 18h -
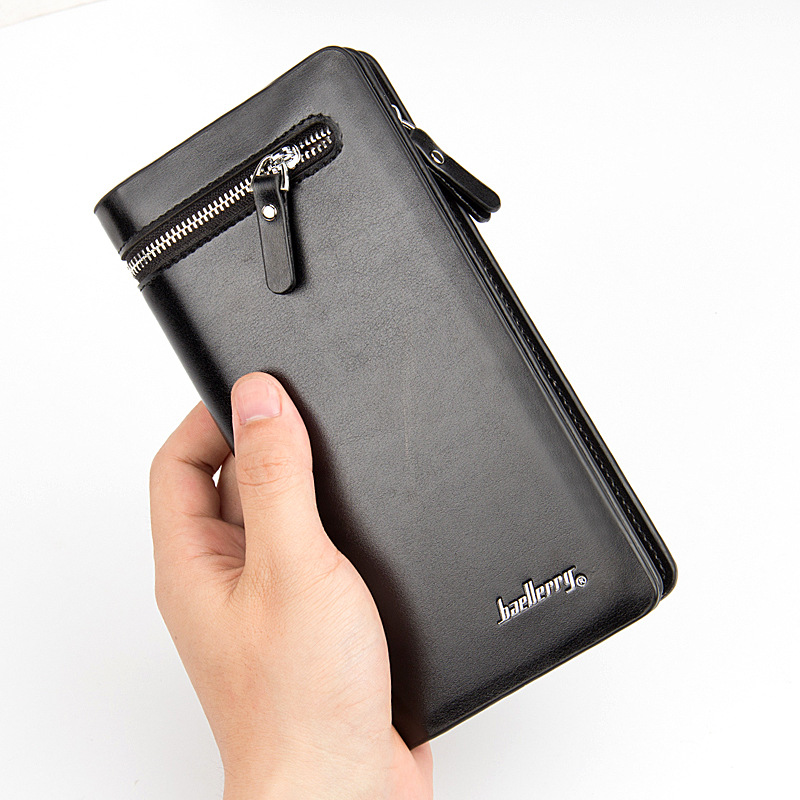
Men Wallet Clutch | Luxury Wallets Phone Bag Capacity
Buy It Now 5d 23h -

Nike Flyknit Trainer 'Black & White' Release Date. Nike SNKRS
Buy It Now 6d 6h -
Louis Vuitton Golf Bag at 1stDibs louis vuitton golf bags, louis
Buy It Now 27d 11h -

Leather Palm Slippers - Brandjou Handmade Footwear, Slippers & Sandals
Buy It Now 4d 16h -
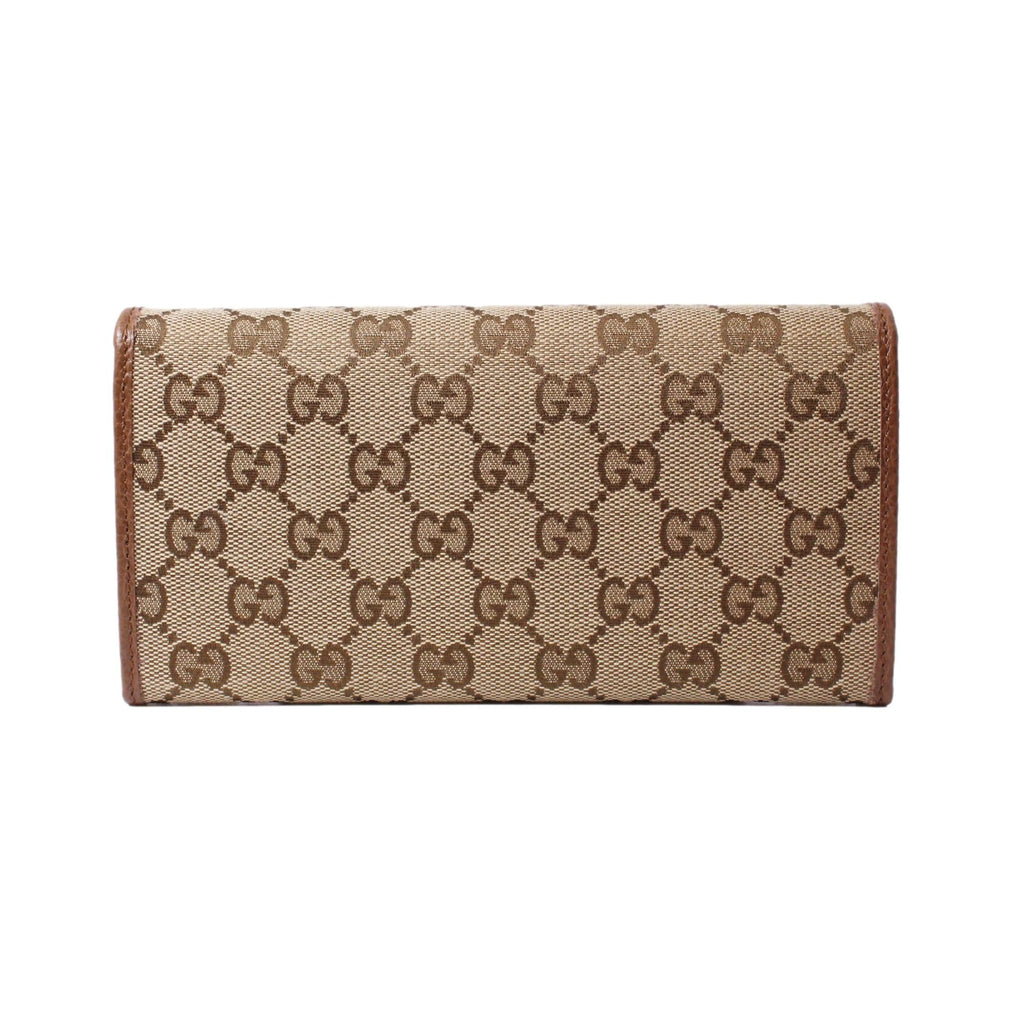
Gucci Original Beige GG Canvas Brown Leather Trim Long Wallet – Queen Bee of Beverly Hills
Buy It Now 17d 20h -
prompthunt: Baroque rap album cover for Kanye West DONDA 2
Buy It Now 21d 17h -
Louis Vuitton Men Dress Shoes Red Bottoms
Buy It Now 12d 11h -
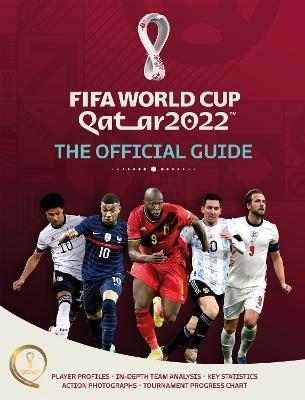
Sport: FIFA World Cup Qatar 2022: The Official Guide
Buy It Now 14d 18h -

Louis Vuitton 2016 Ambler Belt Bag - Farfetch
Buy It Now 20d 8h -

Harry styles and louis tomlinson, 3D
Buy It Now 16d 11h -

Jet set leather wallet Michael Kors Pink in Leather - 21097042
Buy It Now 9d 20h -

Worryfree Gadgets Odash LX06-SLV49 3 in. 49 mm Stainless Steel Band for Apple Watch Ultra - Silver
Buy It Now 15d 5h -

Louis Vuitton Louis Vuitton 18k Rose Gold Malachite Large Blossom Medallion Necklace in Metallic
Buy It Now 9d 5h

